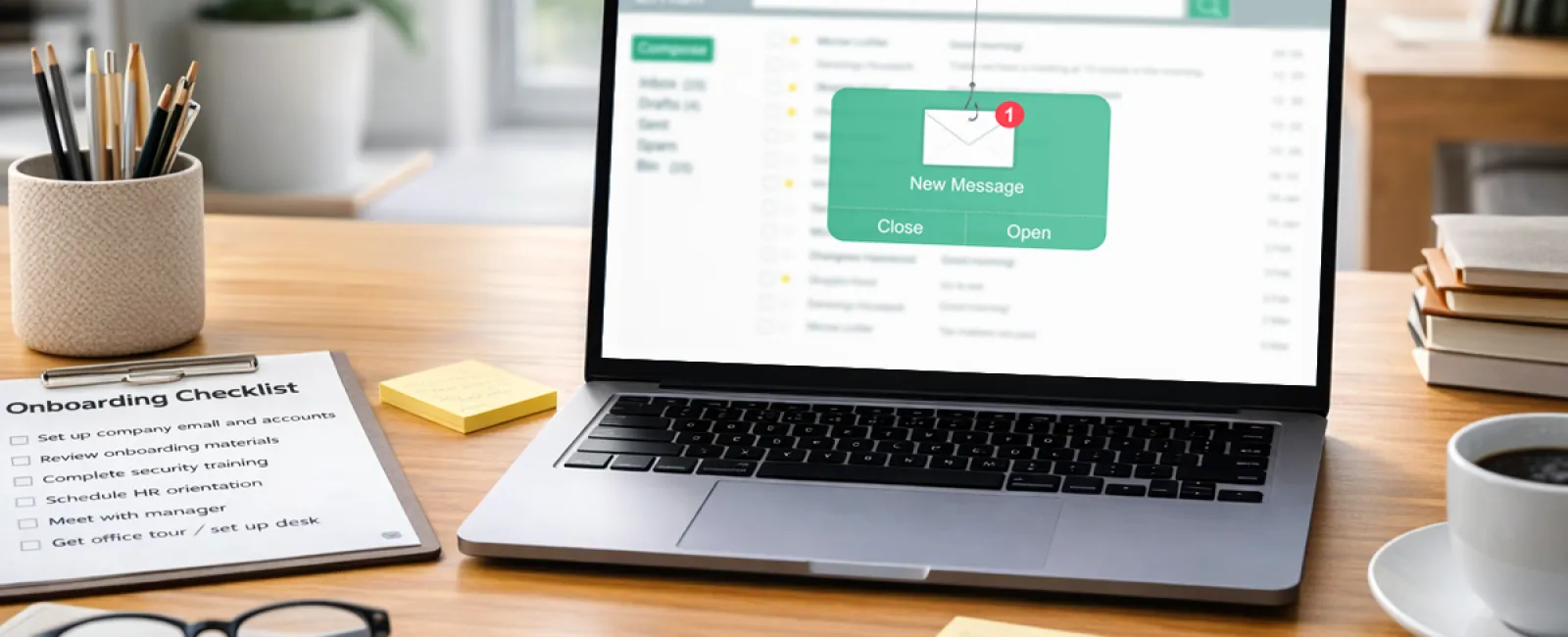
It usually starts with a simple email.
Looks like it came from the CEO.
Name's right. Tone's right. Signature looks normal.
"Hey — need a quick favor. I'm tied up in meetings. Can you handle a vendor payment? I'll fill you in later."
Now picture who's reading that.
Someone on day four.
Still figuring out where things are.
Still trying to make a good impression.
Still not sure what's "normal" yet.
They hesitate for a second…
then they go ahead and help.
And just like that, the money's gone.
The riskiest employee isn't the careless one
It's the new one.
Not because they don't care—
because they do.
They want to be helpful.
They don't want to question authority.
They don't want to look like the person who slows things down in their first week.
That's exactly why these emails work.
They're not trying to trick your most experienced people.
They're going after the ones who are still getting their footing.
And there's always a window at the beginning where everything feels a little uncertain.
Attackers know that.
But here's the part most people miss
The problem didn't start with the email.
It started on day one.
You've seen how first days go:
- Laptop's not quite ready
- Access is still being set up
- Someone says, "just use my login for now"
- Files get saved wherever they can
- Personal phones fill in the gaps
Nobody thinks twice about it.
It just feels like getting through a busy day.
But behind the scenes, a few things are happening:
- Accounts are being shared with no tracking
- Files end up outside your backup
- Personal devices touch company data
- And nobody's clearly said, "here's what to do if something feels off"
So when that email shows up…
There's no system to catch it.
This isn't a training issue—it's a setup issue
Most businesses think, "we just need better security training."
That's part of it—but it's not the core problem.
The real issue is that first week chaos.
When things aren't set up properly, people improvise.
And when people improvise, security gets skipped—without anyone realizing it.
That's the environment those emails are counting on.
What a solid first week actually looks like
You don't need a long presentation or a security handbook nobody reads.
You just need a few things handled before they walk in:
1. Everything is ready to go
No borrowed logins. No temporary fixes.
Their laptop works, their access is set, and they're not guessing their way through the day.
2. They know what "normal" looks like
Quick conversation:
"Would I ever email you asking for a payment like this?"
"Who do you check with if something feels off?"
That alone stops a lot of problems.
3. They know who to ask
This one matters more than people think.
Most first-week mistakes happen because someone didn't want to look inexperienced.
Give them a go-to person.
Make it easy to ask.
Most mistakes aren't rule-breaking—they're guesswork
Nobody wakes up trying to cause a security issue.
They're just trying to do their job… without slowing things down… without asking too many questions.
Especially in that first week.
That's where the risk lives.
If you're bringing people on this year…
This is one of those things that's easy to overlook—until it's not.
If your onboarding is a little scrappy…
or people tend to "figure it out as they go"…
It's worth tightening that up before the next new hire walks in.
Because once that email hits, it's already too late.
Let's make sure your first week isn't your weakest point
We can help you get this dialed in so new hires aren't left guessing—and you're not left exposed.
No overcomplication. Just a smoother, safer setup from day one.
Give us a call at 407-278-5664 or book a quick chat.
And if you know someone about to hire… send this their way.
This is one of those problems that's a whole lot easier to prevent than clean up.